This post is written from a neutral, informational cybersecurity perspective. It explains the concept and the risks involved, as tools like VNHax are often associated with bypassing security systems in potentially unauthorized ways. The VNHax Bypass: What It Is, How It Works, and Why You Should Be Cautious In the ever-evolving cat-and-mouse game of online security, certain tools and terms gain underground notoriety. One such term making the rounds is VNHax Bypass .
Whether you’ve stumbled across it on forums, in cheat repositories, or while troubleshooting locked-down systems, understanding what this tool claims to do—and the risks involved—is crucial. First, let’s break down the name. "Hax" (hacks) combined with "VN" (often referencing Vietnamese cyber communities or specific game engines) generally refers to a set of scripts or executables designed to manipulate software behavior.
Have you encountered a suspicious “bypass” tool? Run a VM and scan it with VirusTotal before even thinking about execution. Better yet, just say no.
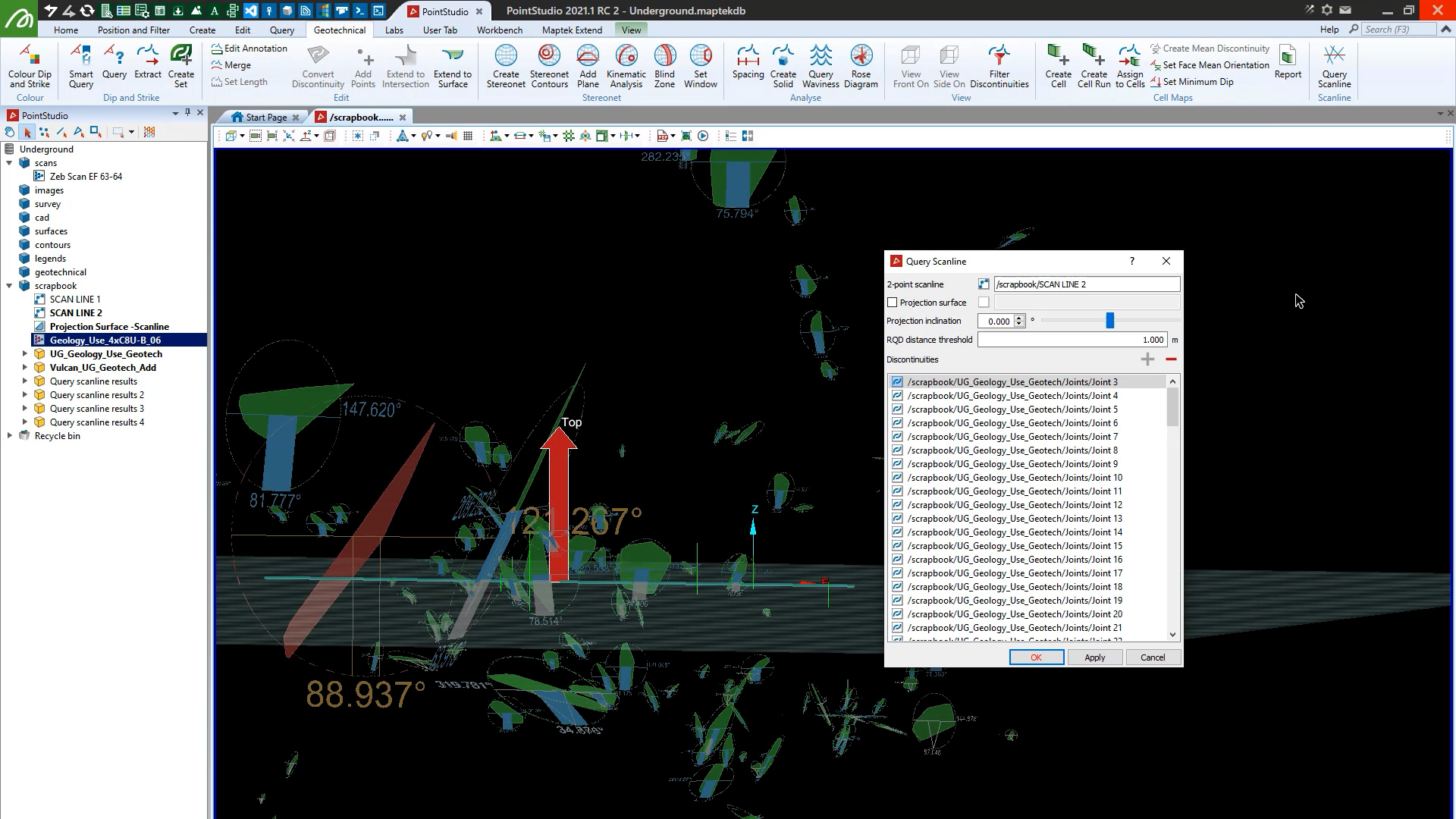
PointStudio 2021.1 features enhanced Inter-Ramp Compliance, performance and stability, supports Maptek R3 mkII laser scanners and enables unwrapping and colouring lines by grade and RQD calculation on scanlines.
This post is written from a neutral, informational cybersecurity perspective. It explains the concept and the risks involved, as tools like VNHax are often associated with bypassing security systems in potentially unauthorized ways. The VNHax Bypass: What It Is, How It Works, and Why You Should Be Cautious In the ever-evolving cat-and-mouse game of online security, certain tools and terms gain underground notoriety. One such term making the rounds is VNHax Bypass .
Whether you’ve stumbled across it on forums, in cheat repositories, or while troubleshooting locked-down systems, understanding what this tool claims to do—and the risks involved—is crucial. First, let’s break down the name. "Hax" (hacks) combined with "VN" (often referencing Vietnamese cyber communities or specific game engines) generally refers to a set of scripts or executables designed to manipulate software behavior.
Have you encountered a suspicious “bypass” tool? Run a VM and scan it with VirusTotal before even thinking about execution. Better yet, just say no.
We use cookies to enhance your browsing experience and analyse our traffic. By clicking "Accept all", you consent to our use of cookies. You can customise your cookie preferences by clicking 'Customise Preferences'.
We use cookies to enhance your browsing experience and analyse our traffic.
Our website may store cookies on your computer in order to improve and customise your future visits to the website. By using cookies, we can track information about your usage of the site and improve your experience with anonymous and aggregated user data.
Review our Privacy PolicyEssential for the website's functionality, without which the site cannot operate smoothly. vnhax bypass
Remember user preferences and choices to provide a more personalized experience. This post is written from a neutral, informational
Collect data on how users interact with the website, helping to improve user experience. One such term making the rounds is VNHax Bypass
Used to deliver targeted advertisements to users based on their browsing behavior and preferences.